Replace SSL Certificate
Overview
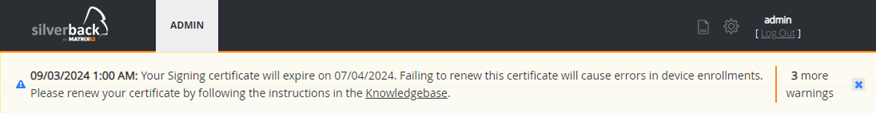
Silverback leverages device management protocols that require an established trust relationship between devices and the server. This allows the server to securely provision and manage your fleet of mobile devices. As an on-premises customer, you have during the initial setup of Silverback, already ordered a valid SSL certificate and stored it in the Internet Information Manager on the Silverback server and at the same time stored the certificate in the Web Settings for profile signing. The first step was done by you using the Silverback SSL Certificate tool and the second step was done manually by selecting the SSL Certificate from the Profile Signing configuration drop down menu in the Web Settings. Depending on the selected validity of the SSL certificate, which is usually 1 year, you will sooner or later reach the point where a warning is displayed in the Silverback Management Console that the certificate is about to expire. At this point at the latest, it is time to apply for a new certificate and update it in Silverback and this guide is intended help you to successfully renew the certificate and ensure that your system remains productive. If you are a cloud customer and have come across this article or received the warning in the console, please read the next section for additional information.
Cloud vs. On-Premises
For cloud customers, the SSL Certificate is automatically renewed quarterly. Occasionally, however, the warning message in the console may overlap with the certificate renewal process and you will receive the warning in the management console. If you are a cloud customer, there is a short Verification for Cloud Customers guide at the end of the article where you can check if the certificate renewal process worked as expected.
If you are hosting Silverback in an on-premises environment, you will of course need to renew the certificate yourself. Please follow the instructions provided in the On-Premises Renewal Process section.
On-Premises Renewal Process
Upload Certificate
- Renew the SSL Certificate by your vendor or buy a new one from another vendor to receive the new *.pfx or *.p12 certificate bundle
- Upload your certificate file to your Silverback Server
Import and Bind Certificate
- Connect via RDP to your Silverback Server
- Click on the Windows Icon in the Taskbar
- Launch the Silverback SSL Certificate Tool
- Switch Certificate Type to Website
- Switch to Import SSL Certificate tab
- Enter your SSL Certificate password, e.g. Pa$$w0rd
- Select Browse and Import certificate
- Locate and select your new SSL certificate
By default, the open wizard is filtered to *.pfx files. Switch to All files in case your SSL certificate is a *.p12 file.
- Press Open
- You should see now in green: SSL Certificate has been imported and bound to the Silverback website.
- Proceed with Verify Permission and Bindings
Verify Permission and Bindings
Read Permission
- Open certlm.msc
- Navigate to Personal > Certificates
- Locate your new SSL certificate and perform a right-click
- Select All Tasks > Manage Private Keys
- Ensure that the Network Service is listed and Read permissions are granted
- Click OK
IIS Binding
- Open Internet Information Services (IIS) Manager
- Expand your Server
- Expand Sites and Select Silverback
- Click in the right pane Bindings
- Double click https
- Click View
- Ensure that your new SSL certificate is shown
- Press Cancel and Close
- Proceed with Update Payload Certificate
Update Payload Certificate
- Open your Silverback Management Console
- Login as Settings Administrator
- Navigate to Payload
- Under Profile Signing Certificate, select your new SSL Certificate
- Press Save
Restart Services
- Open an administrative command prompt or powershell
- Type: restart-service w3svc,silv*,epic*
- Wait until all Services are restarted
Additional Notes
- Please ensure to have updated your new SSL Certificate as well on your Reverse Proxy
- Use the DigiCert® SSL Installation Diagnostics Tool to perform a SSL Certificate Check and validate the TLS chain.
- After replacing your SSL certificate, re-enroll any of your devices and check if you are able to successfully enroll it.
- Perform a refresh inside the Silverback Management Console for an available device and check the device communication inside the Pending Commands
- When you have replaced the SSL certificate, please note that on already enrolled Apple devices, the Signing Certificate inside the Silverback Profile will be shown as expired, but they will still work as usual, as the profile has been signed at the enrollment process. For new devices, the profiles will be signed with the new SSL certificate.
- In case you have issue, e.g. when on Apple devices "Invalid Profile" appears, please review all previously made steps and review Troubleshoot Invalid MDM Profiles
- Add a reminder for the new expiration date in your calendar or enable in Silverback the option to receive Email Alerts to avoid any service interruptions in the future
Verification for Cloud Customers
If you are a cloud customer and have received the console warning, you can assume that your certificate has usually been updated automatically. However, we would like to take this opportunity to show you how to ensure that the process has worked.
- Open your Silverback Management Console
- Depending on the browser you are using, look for the button next to the URL bar that displays page's security information
- For demonstration purposes, we will use Chrome as an example
- Press the View site information button in your URL bar. It is indicated by a settings icon. In Firefox and Edge it is most likely a lock button
- Now expand the Connection is secure option and press the Certificate is valid label
- Check the Issued On timestamp in the Validity Period section. It should show a date that is no more than a few days old
- This already indicates that the certificate has been generated and renewed
- As the SSL certificate is used to sign profiles, you can perform another check to verify that the database update worked also as expected
- To do this, navigate to the Details tab in the Certificate Viewer section (where you checked the timestamp)
- Click Export and save the file as certificate.cer, for example, on your desktop.
- Now double-click on the certificate and navigate to the Details tab and scroll down to the Thumbprint information
- From the Silverback Management Console, login as Settings Administrator
- Navigate to Payload and expand the drop down list for Profile Signing Certificate and check if the thumbprint matches
If the certificate is stored both in the browser and in the Settings Admin, then everything is fine and worked as expected. If, contrary to expectations, you either notice in the first step that the certificate has not been renewed or in the second step that the certificate has not been properly updated in the profile signing section, please contact our support.
Additional Notes
- When the SSL certificate has been replaced, please note that on already enrolled Apple devices, the Signing Certificate inside the Silverback Profile will be shown as expired, but they will still work as usual, as the profile has been signed at the enrollment process. For new devices, the profiles will be signed with the new SSL certificate.