Exchange Protection Allow managed devices
Exchange Protection
When enabling the Quarantine Mode in your Exchange, all current connected devices will be automatically moved into the Quarantine Mode. As Silverback is moving managed devices with their Exchange ActiveSync identifiers to the ActiveSyncAllowedDeviceIDs list for specific users when an Exchange ActiveSync Profile will be installed on the device, this guide will help you to allow your current managed devices without removing and reassigning the Exchange ActiveSync Profile to your devices fleet after enabling the Quarantine Mode. This is typically a challenge for Administrators, when Silverback and Exchange is already in use (before activating the Exchange Protection) and users are already connected to ActiveSync. As a reassigning of the Exchange ActiveSync profile would cause that users would be prompted for re-entering their password (if no certificate based authentication used), this guide will ensure to make the transition without that need. During this guide, we will export all known Exchange ActiveSync identifiers either from the Hardware Summary Export or from your Silverback database and exporting them into an *.csv File. Afterwards we will connect from your Silverback or Cloud Connector Server (or local machine if Modern Authentication is used) to Exchange Online and review a user's mailbox, before we will execute the PowerShill script, which is attached to this guide. The exported *.csv will provide us the source for the target EAS identifiers, that we want to move into the ActiveSyncAllowedDeviceIDs list. The Powershell script will identify based on the identifiers, the corresponding mailbox names and will allow all devices for specific users in a bulk action. After executing the script we will review if a contained EAS identifier from the *.csv will be added to the ActiveSyncAllowedDeviceIDs list. As a result, all of your managed devices in Silverback will be allowed and all not managed devices will require a manual administrative task to grant the access separately.
Export ActiveSync Identifiers
Exporting ActiveSync Identifiers can be achieved in two different ways. On-Premises customers can use an SQL Query Export and Software as a Service customers can use the Hardware Summary export.
SQL Export
- Connect to your SQL Server
- Execute the following query on your SQL
SELECT [Mdm_EASDeviceIdentifier] FROM [Silverback].[dbo].[DeviceLatestInfos] WHERE Mdm_EASDeviceIdentifier is not NULL and DeviceId in (select DeviceId from Devices where DeviceStatusId=2 and Active=1)
In case you have currently blocked devices, these are not part of the result. When they will be moved from blocked to managed, the Exchange ActvieSync Profile will anyway be re-applied to the device and then the device will be automatically moved to the ActiveSyncAllowedDeviceIDs list through Silverback.
- Perform a right click in the result section
- Export the results into a *.csv file into a temporary location, e.g. as EASIdentifiers.csv
Hardware Summary Export
Added in Silverback 21.0 Update 2
- Open your Silverback Management Console and login as an Administrator
- Navigate to Dashboard
- Click Export below Hardware Summary and open the downloaded Hardware Summary.xlsx
- Enable Filtering and set the Filter for column Device Status to Managed
- Scroll to the right and locate column EAS Device ID and set the filter to exlude -
- Now select all remaining Exchange ActiveSync identifiers and copy them into your clipboard
- Open Notepad or any TextEditor and paste all identifiers
- Save the results into a *.csv file into a temporary location, e.g. as EASIdentifiers.csv
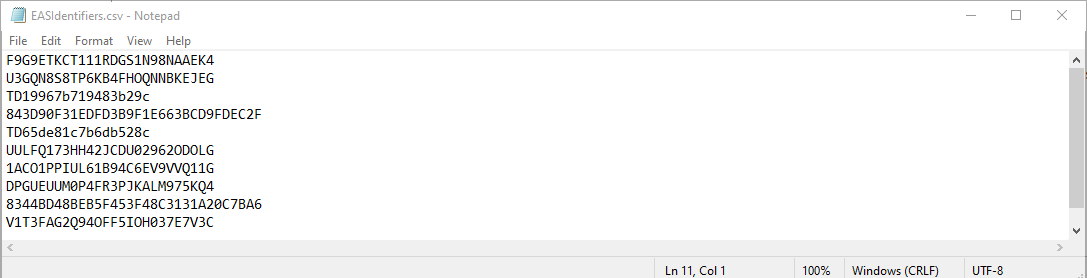
- Your outcome should look like this
Prepare Script Execution
- Connect to your Silverback or to your Cloud Connector server
- Create a new folder, e.g. C:\Temp
- Copy the exported EASIdentifiers.csv file into this folder
- Add the following PS_AddDevicesToUsersAllowedList.ps1 into this folder
This script is not supported for Exchange 2010. In newer versions, the commands has been changed and Exchange 2010 is out of support by Microsoft.
Connect to Exchange Online
Depending on your authentication setup for Exchange Online, the connection methods are slightly different.
Connect with Modern Authentication
- On Premise Customers: Open PowerShell on your Silverback Server
- Cloud Customers: Open PowerShell on your workstation, where you performed the Exchange Protection Integration with Modern Authentication
- Run the following adjusted command:
Connect-ExchangeOnline -CertificateThumbPrint "502ca2f6f74bc5ea7b21b6a18182da8209a4f266" -AppID "e9e621e9-cc90-4b48-a9d4-43ee7e6c4e4b" -Organization "imagoverum.onmicrosoft.com"
For Cloud Customers, the EXO V2 Powershell Module must be installed and the certificate must be present on the local machine.
-
Proceed with Review an existing mailbox
Connect with Basic Authentication
As this guide is intended for Exchange Online, adjust the session string for connecting to Exchange Server 2016 and 2013
- Now Open PowerShell on your Silverback or Cloud Connector Server
- Run the following command
$UserCredential = Get-Credential
- Enter your Service Account, e.g. silverback_exchange@imagoverum.com
- Enter your updated password, e.g. Pa$$w0rd
- Click OK
- Create a new Session:
$Session = New-PSSession -ConfigurationName Microsoft.Exchange -ConnectionUri https://outlook.office365.com/powershell-liveid/ -Credential $UserCredential -Authentication Basic -AllowRedirection
- Import now the session with
Import-PSSession $Session -DisableNameChecking
Review an existing mailbox
- Execute the following command, to check the ActiveSyncAllowedDeviceIDs values for a specific user
Get-CASMailbox -Identity tim.tober@imagoverum.com | fl *ActiveSync*
- Review currently quarantine devices for a specific user
Get-MobileDevice -Mailbox tim.tober@imagoverum.com -Filter {DeviceAccessState -eq 'Quarantined'}
Execute PowerShell Script
- Navigate now to your folder location, where the PowerShell script and the EAS Identifiers are located
cd C:\Temp
- Now execute the PowerShell command as following:
.\PS_AddDevicesToUsersAllowedList.ps1 -PathToCsv C:\Temp\EASIdentifiers.csv
Review existing mailbox changes
- Execute the following command, to check the ActiveSyncAllowedDeviceIDs values for a specific user
Get-CASMailbox -Identity tim.tober@imagoverum.com | fl *ActiveSync*
- ActiveSyncAllowedDeviceIDs values should be now increased with an Exchange ActiveSync Identifier from the EASIdentifier.csv file