Release Notes Silverback 21.0
About This Release
Matrix42 Silverback 21.0 provides new and improved features that have been implemented. During the development of this version, we have been focusing on valued feedback from our customers and partners in order to provide an ideal feature selection.
Overview
New Features
Endpoint Security Features for Microsoft Defender
Android Enterprise
Email Notifications
Apple Management
New Improvements
New Changes
New Features
Endpoint Security Features for Microsoft Defender
Silverback 21.0 includes the following new Endpoint Security Features for Microsoft Defender.
Defender Antivirus Remediation
With Silverback 20.0 Update 2 we gave Administrators new capabilities to review and control the Windows Defender Antivirus information and configuration. One part of this Defender Antivirus is to detect Threats on the device, e.g. when a malicious software has been detected or the device has been tampered. With Silverback 20.0 Update 3 we brought the capability into our UUX to show detected threats. With the Remediation feature in Silverback 21.0 we provide settings to define a default action for detected threats.
| Remediation | Options |
|---|---|
| Configure Detected Threat Actions |
|
| Low Threat |
|
| Moderate Threat | |
| High Threat | |
| Severe Threat | |
| Specify Removal of Items From Quarantine Folders |
|
| Time period (in days) | e.g. 30 |
Defender Antivirus Scan Exclusions
Administrators can configure to exclude certain files, folders, processes, and process-opened files from Microsoft Defender Antivirus scans. Such exclusions apply to scheduled scans, on-demand scans, and always-on real-time protection and monitoring. Exclusions for process-opened files only apply to real-time protection. With this Feature Administrators can specify to trust a file, file type, folder, or a process that Windows Security has detected as malicious, which will result in a stop for Windows Security from alerting the users or blocking the program.
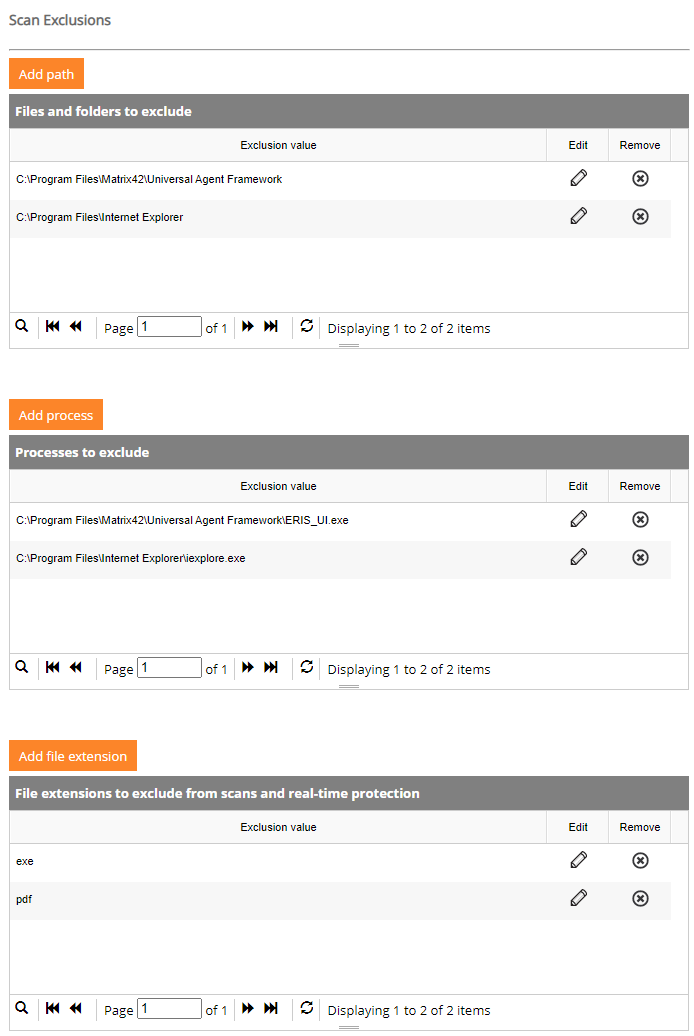
Controlled Access Folder Configuration
Controlled folder access in Windows Security reviews the apps that can make changes to files in protected folders and blocks unauthorized or unsafe apps from accessing or changing files in those folders. Add allowed applications that gain access to protected folders and can make changes without a Windows Defender information or add additional folders that needs to be protected.
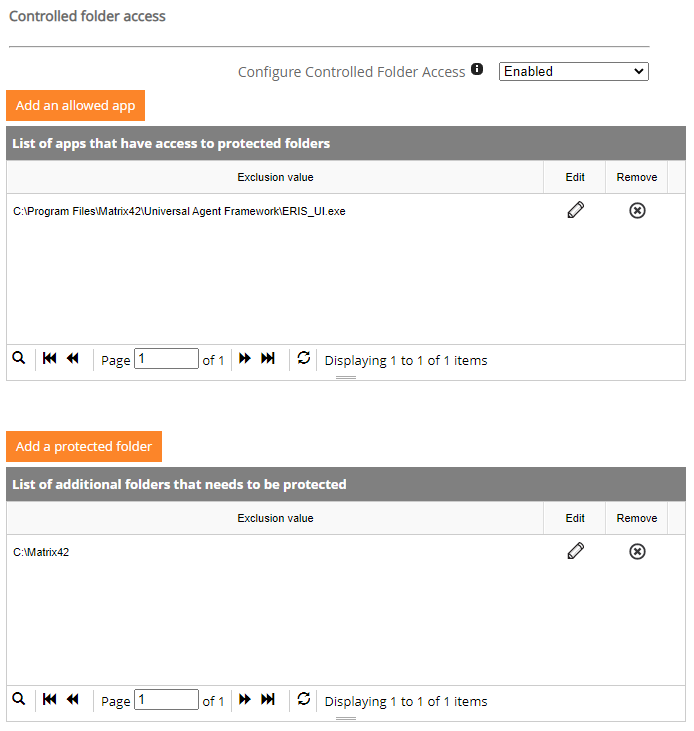
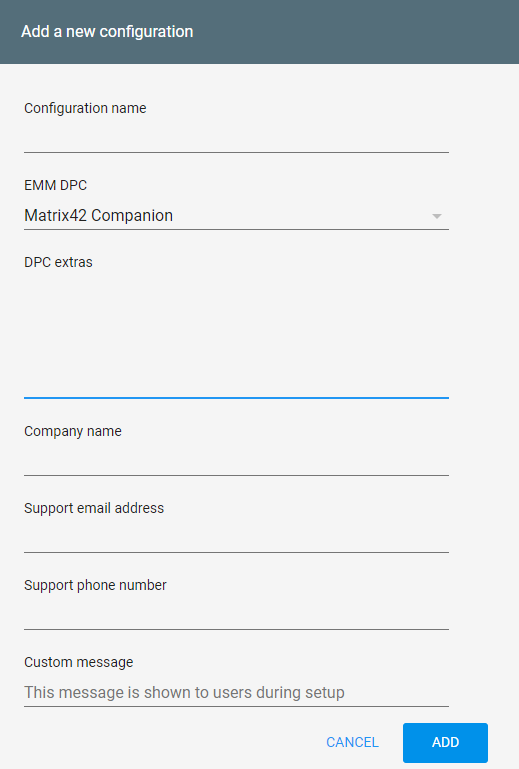
New Enrollment Options for Zero Touch and Knox Mobile Enrollment
Currently the enrollment process on Android Enterprise Corporate Owned devices (Device Owner) devices with the Zero Touch or Knox Mobile Enrollment experience is based on a second factor (QR-Code or Manual entered credentials), which users are representing during the final enrollment step within the Companion application. The Zero Touch Enrollment on Android and/or the Knox Mobile Enrollment for Samsung devices grants the possibility to Administrators to pre-configure device policy controllers, like Matrix42 Companion, in a specific JSON format. Our new Companion Version for Silverback 21.0 supports now these new mechanism to remotely configure (enrollment) settings for users, which will ensure a smooth enrollment performed on the used devices. These options grants the possibility to add in the configuration the address of your Silverback Self Service Portal, so that users will be forwarded directly to the Self Service Portal inside the Companion and perform the Enrollment with Active Directory or Azure Active Directory credentials. Additionally you can use this mechanism to provide a fully authenticated device enrollment for non-personalized devices in combination with the Bulk Staging Mode.
Options
| Platform | Custom Configuration |
|---|---|
| Android Zero Touch Enrollment | Enrollment With Self Service Portal |
{"android.app.extra.PROVISIONING_ADMIN_EXTRAS_BUNDLE":{"server_url":"https://silverback.imagoverum.com"}}
|
|
| Android Zero Touch Enrollment | Enrollment with preset Authentication |
{"android.app.extra.PROVISIONING_ADMIN_EXTRAS_BUNDLE":{"server_url":"https://silverback.imagoverum.com", "user_name":"tim.tober@imagoverum.com","otp":"4444"}}
|
|
| Samsung Knox Mobile Enrollment | Enrollment With Self Service Portal |
{"server_url":"https://silverback.imagoverum.com"}
|
|
| Samsung Knox Mobile Enrollment | Enrollment with preset Authentication |
{"server_url":"https://silverback.imagoverum.com","user_name":"tim.tober@imagoverum.com","otp":"4444"}
|
|
Configuration
| Android Zero Touch - Add your configuration in the DPC extras section | Knox Mobile Enrollment - Add your configuration to Custom JSON Data |
 |
 |
New Email Notifications
With Silverback 20.0 Update we provide two new E-Mail templates and corresponding Notifications to Administrators.
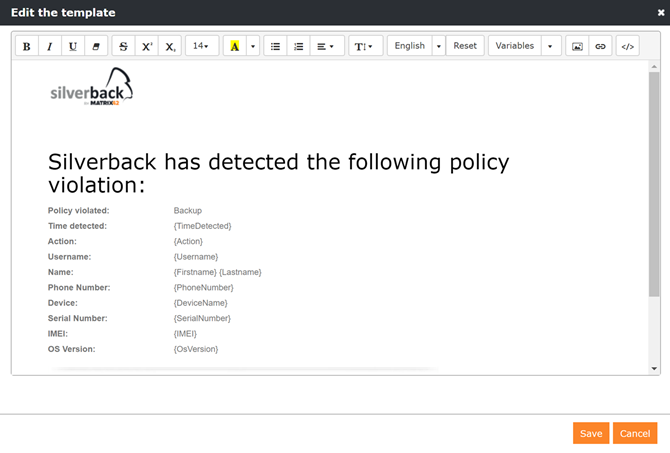
Detected Restore from Backup
Administrators will receive a notification via E-Mail in case a managed Apple device has been restored from a backup, which leads to a policy violation if Allow Restore from Backup is not allowed in the Admin sections. You will find the new Backup Violation Alert Email Template located under Admin > Email Templates.
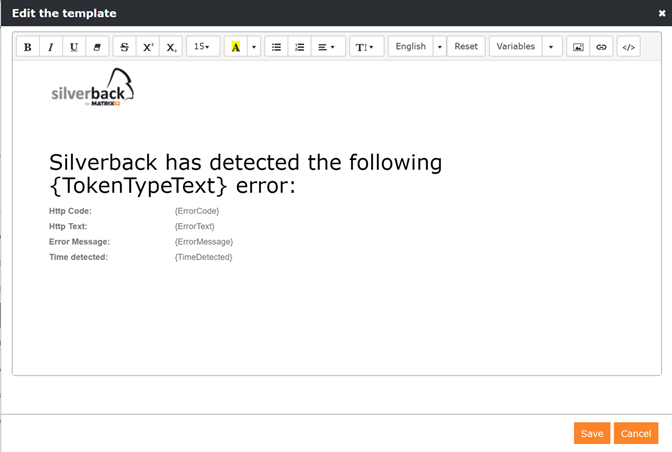
Revoked Deployment Program or Volume Purchase Program Tokens
Apple Business Manager rejects from time to time tokens for the Volume Purchase or the Device Enrollment Programs without notifications for Administrators. In this case Administrators are only recognizing this when the syncs are not working anymore which is shown only in the Logs. To provide Administrators additional information about this issue, we will send in this cases a Notification Email scheduled every night and first when the issue appeared.
After receiving E-Mails, e.g. for Device Enrollment Program Program with the Error Message: oauth problem advice, please renew your token. Please refer to the Apple Deployment Programs II: Configure Deployment Programs for additional information.
New Management Features for iPods
With Silverback 21.0 we updated the available feature subset for iPods. This includes the following profiles and features:
- Wallpaper
- Notification Settings
- Lock Screen Message
- Home Screen Layout
- Disable MAC Address Randomization for Wi-Fi
- Tag based App Management
New Improvements
Installer
- After installation and updates the Default Browser will now be used
- Silverlight has been removed from installing prerequisites
- Microsoft Access Database Engine 2010 has been removed from installing prerequisites
- After the setup a backup of the current admin web.config will be automatically done and saved as AdminBackUp.config in the root folder
- For each web service an additional web.config backup will be done automatically and saved as web.config.2020-01-01_14-32-58.bak
- Fix for not working change database connection option on Database Installation screen
Management Console
- Added recent OS Versions for all platforms
- Added select/unselect all button to OS Version and Hardware
- Optimized pagination for pending enrollment
- Updated EPiC settings name in Companion Policy section
- Optimized positioning of Passwords in Wi-Fi Profiles
- Fix for not working Save & Close button in sections
- Added Save & Close buttons in missing sections
- Updated EPiC Certificate Warning to correct new name Companion Push Notification Service Certificate
- Optimized Failed to get MDM Profile error screen
Apple Device Management
- Bulk Messages through Tags are now based on the new HTTP/2 APNs approach
- Added supervised information for macOS devices
- Several recently added security related profiles will now remain on macOS devices when devices are blocked
- Solved the problem of default 30 days Operating System deferral for macOS devices
- User Enrollment Clear Passcode action is now greyed out according to availability for specific management type
- Moved position of Device to Device Migration in Device Enrollment Program section
- Adjusted Tooltip for MAC Address Randomization due to recent changes in iOS 14
- Last DEP Refresh information timestamp is now shown with AM or PM
- Updated styling of Volume Purchase Program button
- Volume Purchase Program related Logs are now completely represented in the corresponding section
- Increased length of Refresh Token for Device for new HTTP/2 approach
- When you remove a Volume Purchase Program application from a macOS tag, the application will now be uninstalled and the license will be unassigned
Windows 10
- Applications are now reinstalled after devices return from blocked state. In some scenarios some applications started only after an additional refresh
- Added handling to define proper security protocol for requests to the Windows Push Notification Services
- Updated Microsoft Defender Antivirus settings with additional grouping and relations
- Added for several Restrictions groups not configured values
- Solved issue with unable to process with request when certificates are added to Certificate Profile without private key
Android Enterprise
- Added separate Android Enterprise logging category
Authentication Providers
- Added import of E-Mail , Firstname and Lastname values from Authentication Providers
Cloud Connector
- Improved automatic connection reestablishment after system exceptions
- Added Service Description
Changes
- Updated Service Bus Message Model to 5.6.1
- Updated Service Bus Adapter to 6.5.0
- Updated Service Bus Contracts to 1.3.0