Patch Management Scan Package cancels with error "Signing certificate validation failed"
Problem
The following error appears in the PM_ScanTrace.log if the client does not have the necessary certificates to
validate the patch catalog:
patchScanEngine::CScanner92::CScanner92InterfaceImpl::Initialize invalid operation: class STCore::CInvalidOperationException at Opc.cpp:1466: Signing certificate validation failed in 'C:\EmpirumAgent\PatchManagement\Repository\Catalog\WindowsPatchData.zip'.
If the two certificates aren't installed on the client; the scan will continue to fail.
Solution 1 – Group Policy
- Use a Group Policy to deploy updated Certificates as outlined in https://technet.microsoft.com/en-us/library/cc770315
- If they are not present: Install them each manually by double-click on the .cer, click Install Certificate > leave Automatically select... enabled > Next > Finish
- Check the store outlined above and ensure they are present
Solution 2 – Manual Update
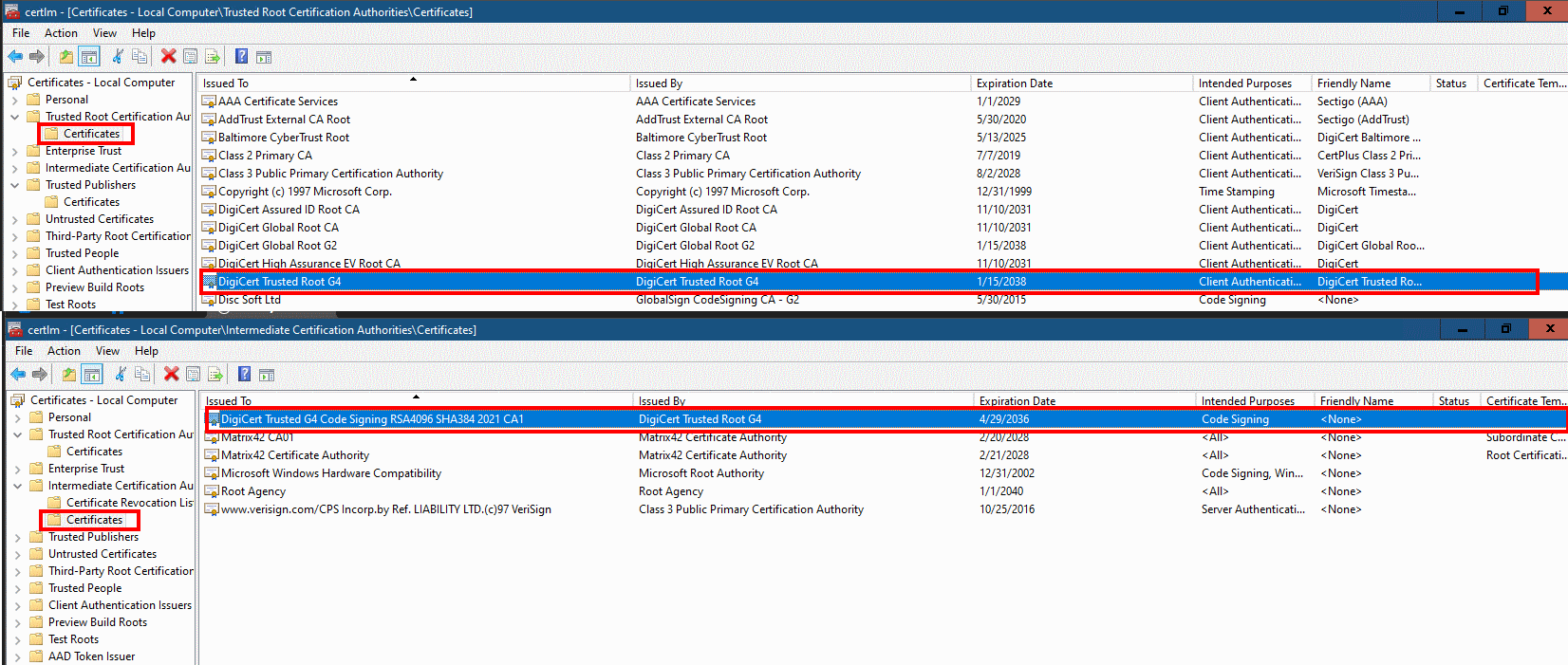
Manual installation as follows proves to be efficient on the clients via Start > Run > MMC.exe;
open Console Root > Certificates (Local Computer) and confirm if the certificates exist in the following locations
- DigiCertTrustedRootG4: Trusted Root Certification Authorities\Certificates https://cacerts.digicert.com/DigiCertTrustedRootG4.crt
- DigiCertG4CodeSigningCA : Intermediate Certification Authorities\Certificates
https://cacerts.digicert.com/DigiCertTrustedG4CodeSigningRSA4096SHA3842021CA1.crt