OneDrive Tenant Configuration for Microsoft 365 Service Connection
To register DWP for Microsoft 365 Service Connections integration, start with registering ESMP at the Microsoft identity platform.
-
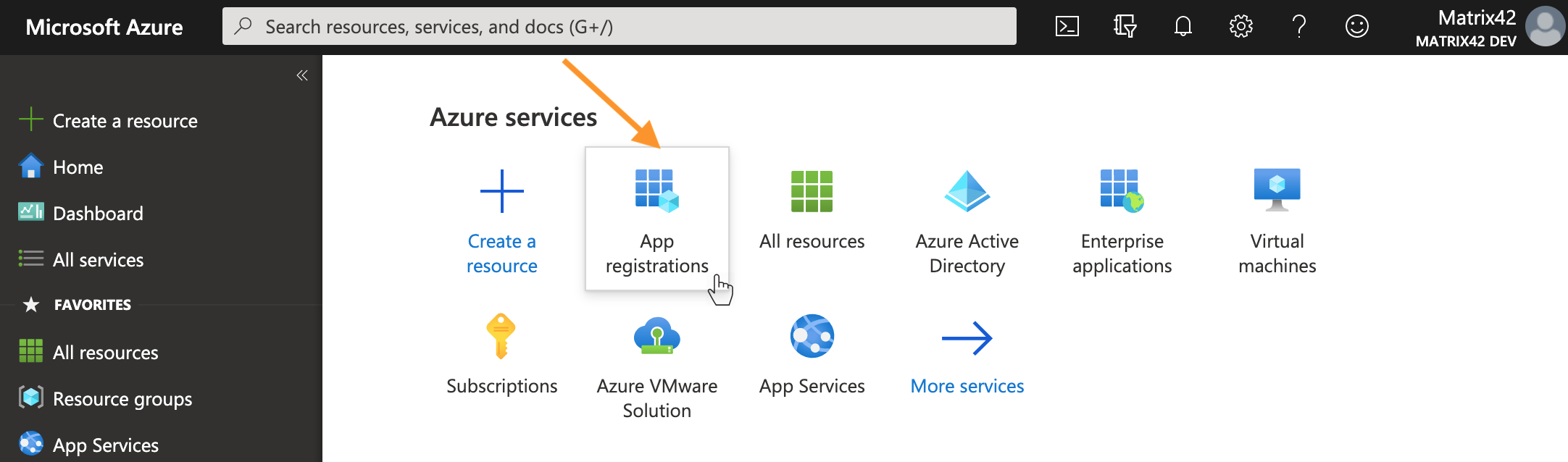
On the Microsoft Azure Portal home page, go to the Azure services section or use the Search resources search bar and open App registrations:
Microsoft Azure Portal: App registrations - Provide a Name for the application. The DWP users will see the display name when applying the Setup Authentication for the configured Service Connection.
- Choose the Supported account types
- Add a Redirect URI: select Web and enter Redirect URI, for instance, https://{your_domain_name}/wm/externalAuth/redirect.html.
- Click Register.
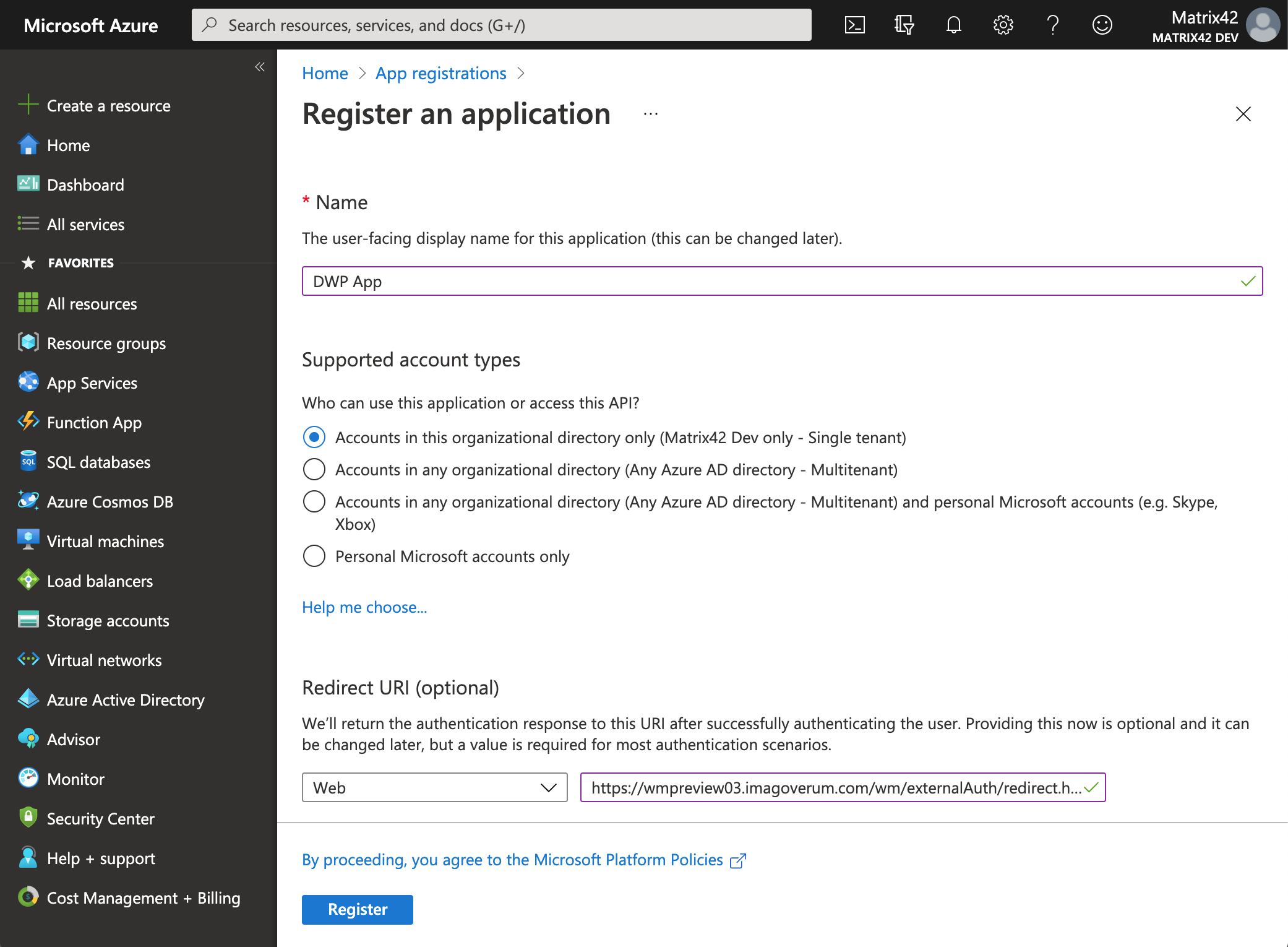
Microsoft Azure Portal: Name, Supported account types, and Redirect URI
- Click on your new App Registration, for instance, DWP App, go to the Overview section. Here you can find the following data for the OneDrive Tenant configuration in DWP Service Connections:
Microsoft Azure Portal Application Overview field name ESMP Tenant configuration field name Application (client) ID Tenant Directory (tenant) ID Client ID
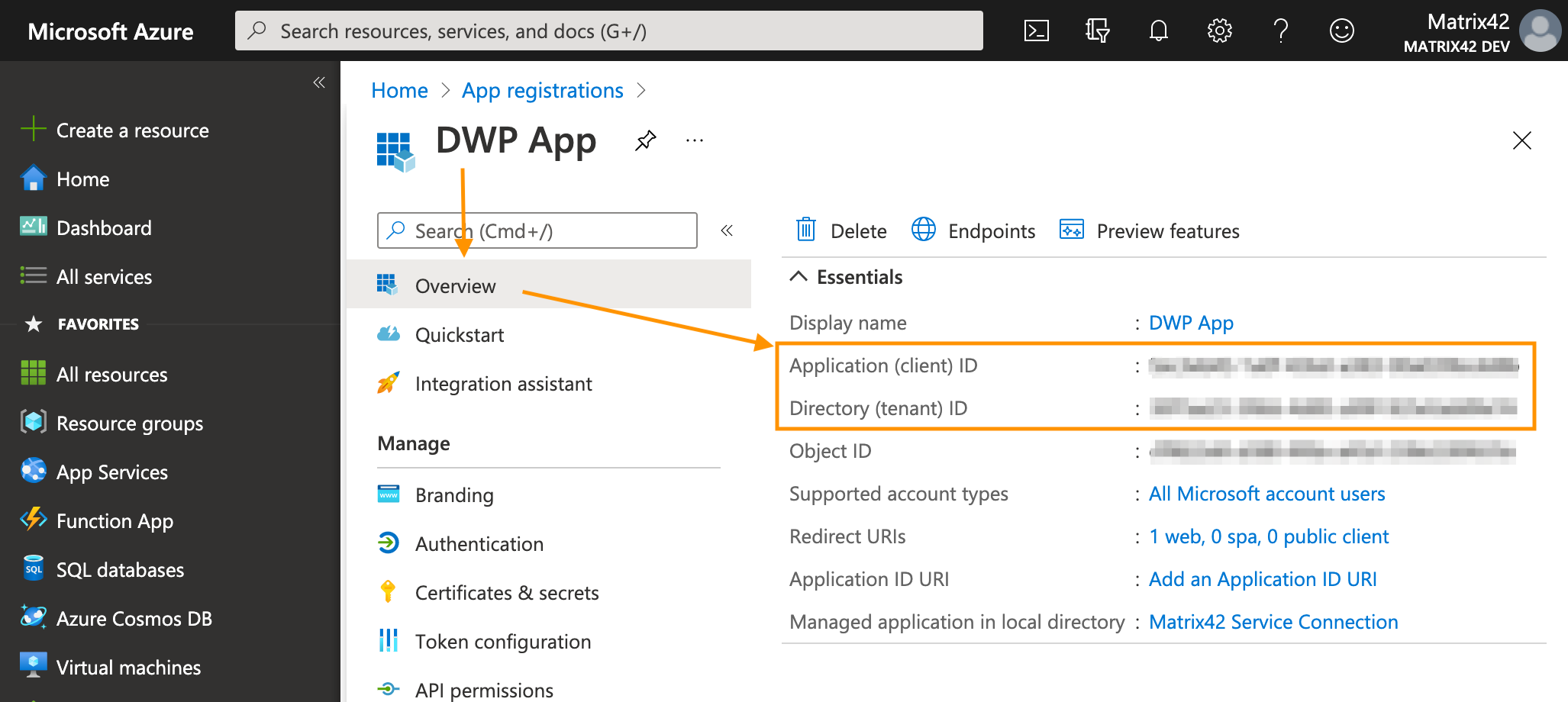
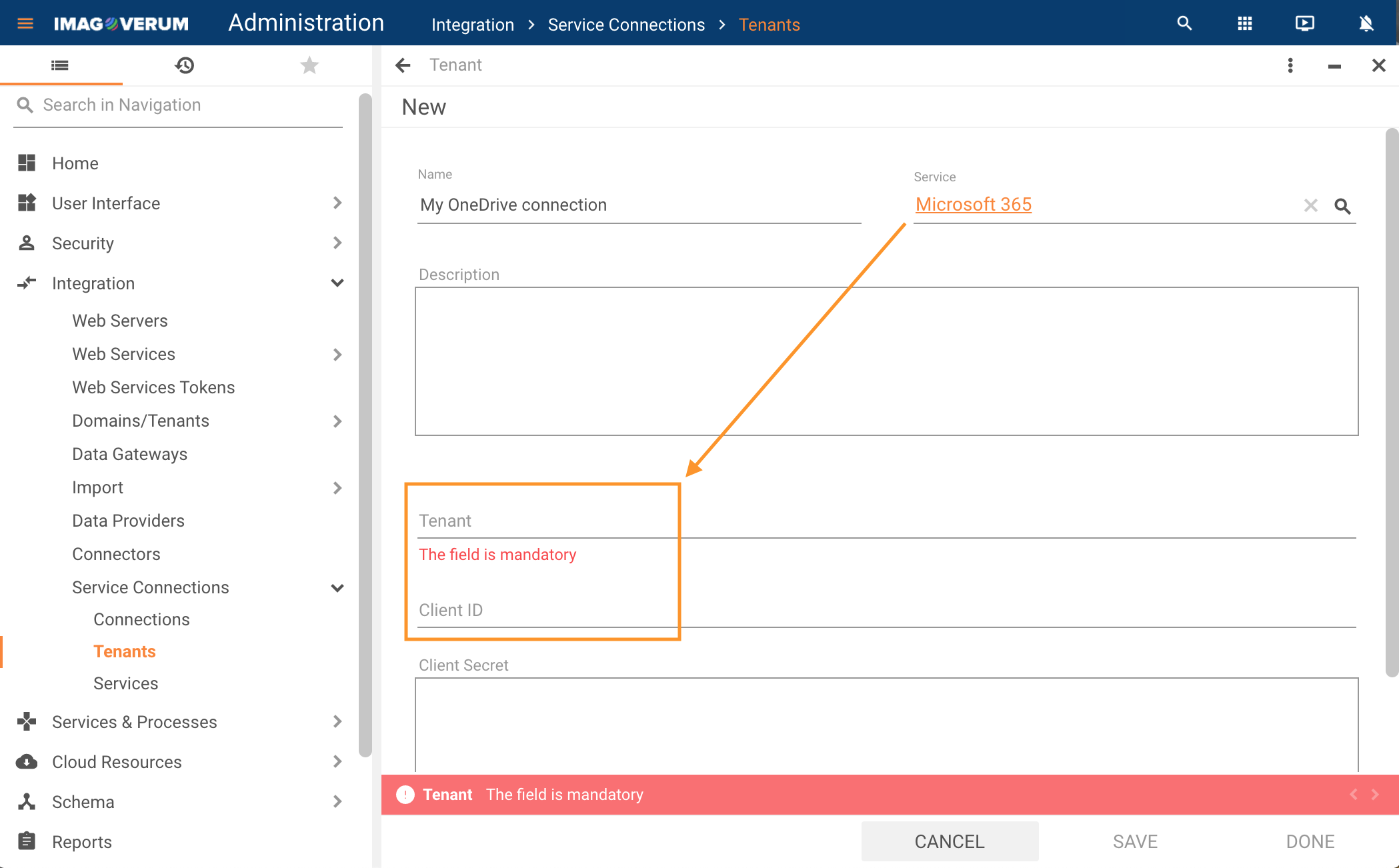
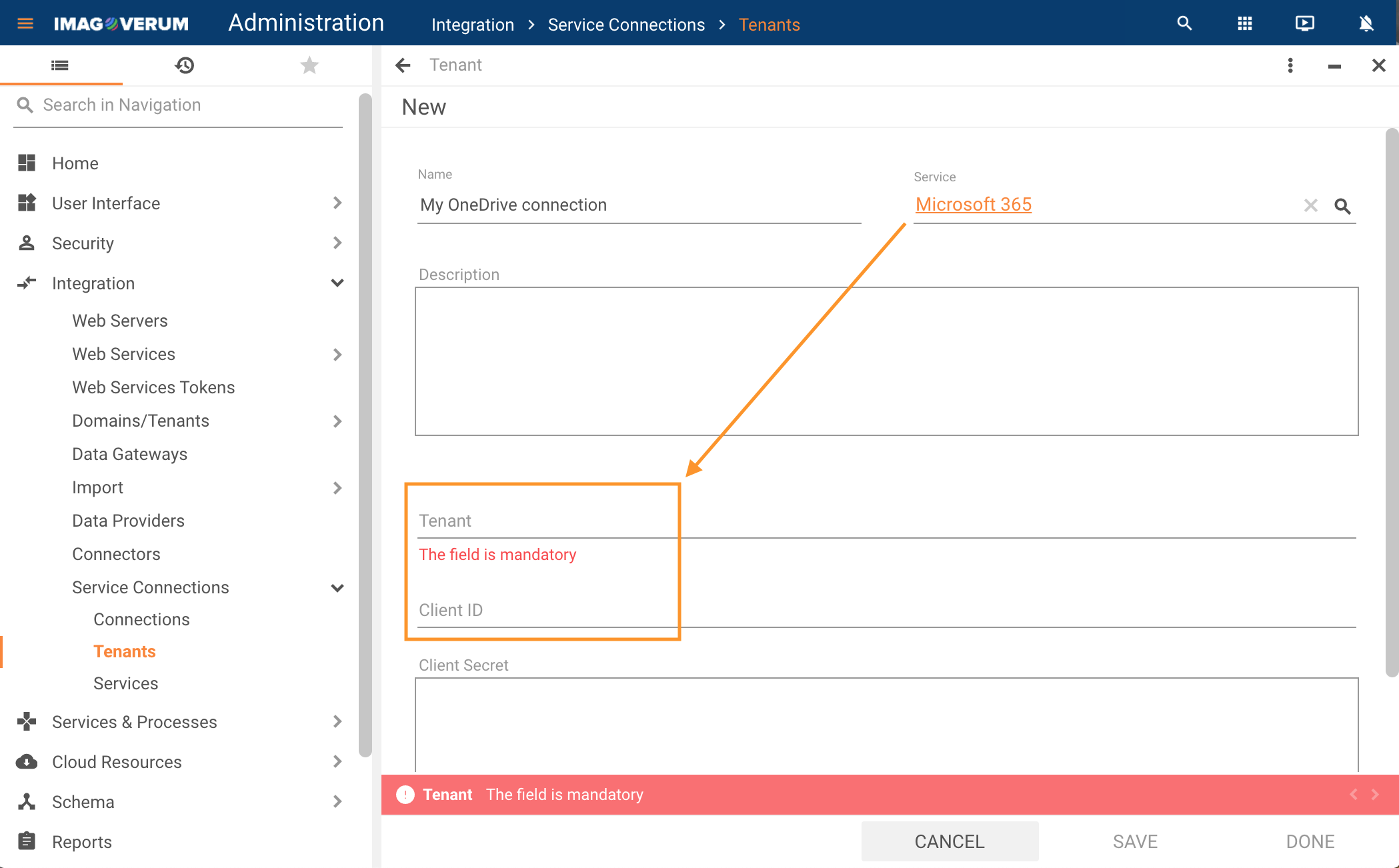
Enter the data to the corresponding fields in the Administration application → Integration → Service Connections → Tenants configuration:
- Add Client Secret: in your registered application, go to the Certificates & secrets section → click + New client secret → provide a Description → copy the Value of the generated Client secret, as it will be encrypted and shown on the Certificates & secrets section as suggested on the image below.
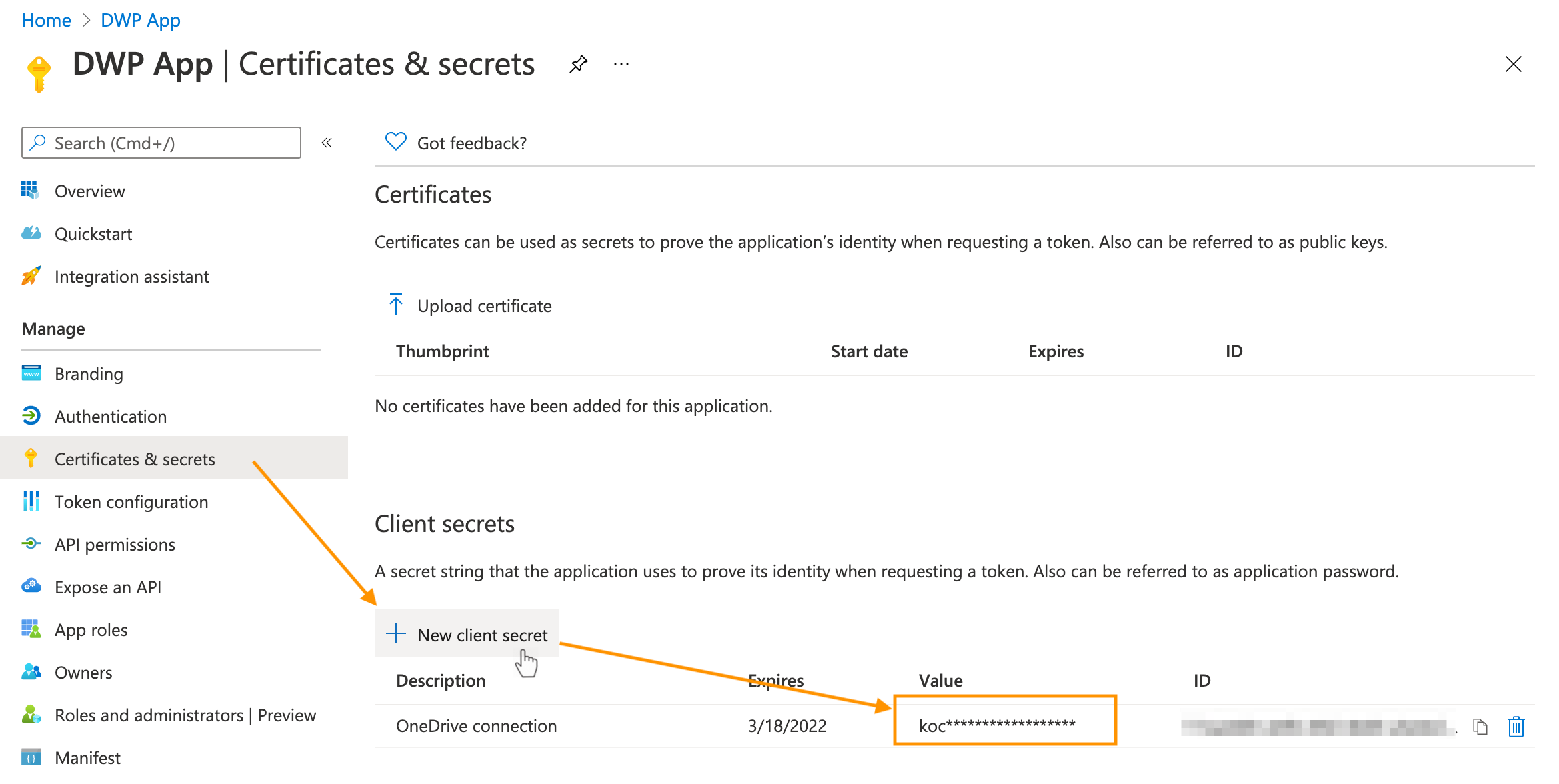
- Enter the copied Client secret value in the OneDrive Tenant configuration in DWP Service Connections:
For more information about App registration, see also Microsoft Documentation Quickstart: Register an application with the Microsoft identity platform.
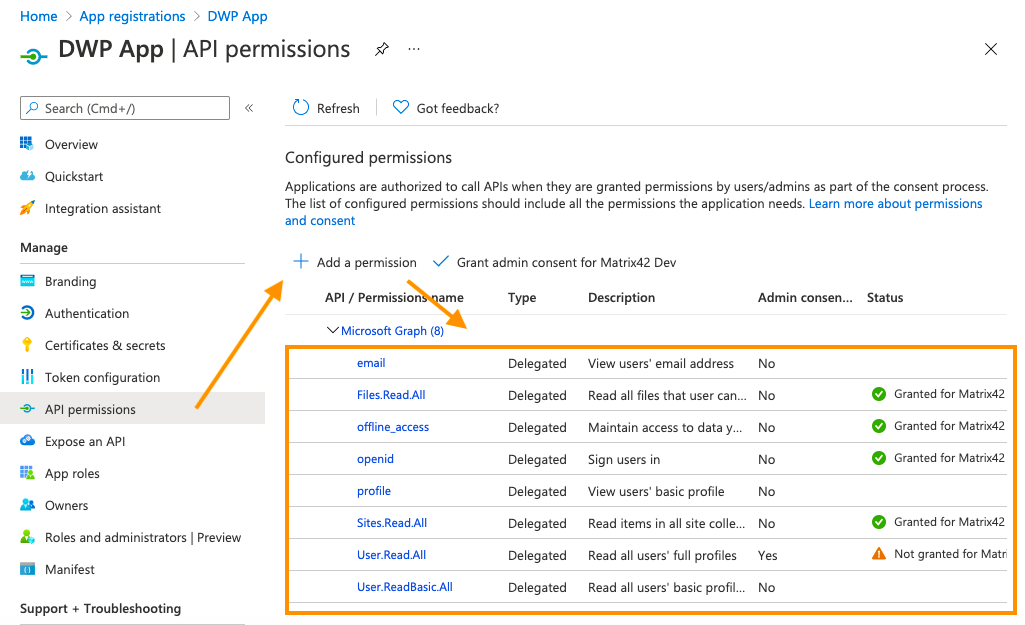
- Add API permissions: in your registered application, go to the API permissions section → click + Add a permission → choose Microsoft Graph → Delegated permissions → select necessary permissions from the suggested list → click Add permissions:
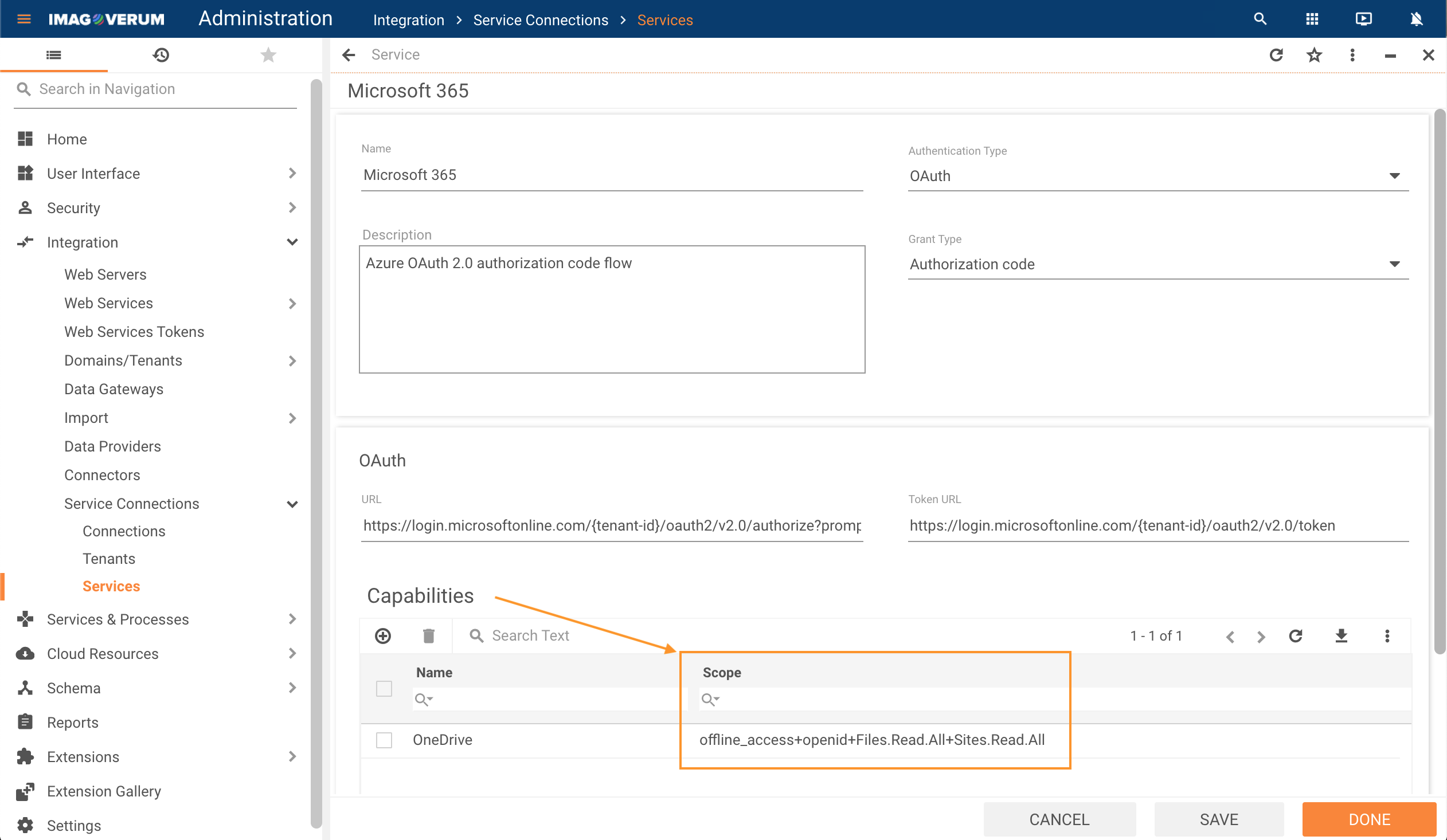
- Add the corresponding permissions to the Scope area for your Service provider configuration: open Administration application → Integration → Service Connections → Services → Microsoft 365 → Capabilities section → Scope:
For more information on how to add a scope, see also Microsoft Documentation Quickstart: Configure an application to access a web API.